Detecting Cyber Threats- SMBs
How to detect cyber threats: A practical guide for SMBs

A small manufacturing company in Ohio discovered a breach only after a vendor called to report strange file requests coming from the company’s shared drives. By then, attackers had spent three weeks inside the network, quietly copying contracts and pricing data. The total cost, including forensics, legal fees, and lost contracts, exceeded $400,000. That scenario is not unusual. For small and mid-sized businesses (SMBs), a missed cyber threat carries severe financial and reputational consequences. This guide walks you through actionable detection steps, essential tools, and expert strategies so your organization can identify threats early, even with limited IT resources.
Table of Contents
Understanding the modern cyber threat landscape
Preparing the right monitoring environment
Step-by-step detection: Key techniques and real-world methods
Aligning detection with frameworks: Mapping with MITRE ATT&CK
Why relying on basic alerts is no longer enough
How tekrisq helps you stay ahead of cyber threats
Frequently asked questions
Key Takeaways
PointDetails Continuous monitoring Setting up the right monitoring tools helps catch threats before they cause real harm.Framework alignmentMapping to frameworks like MITRE ATT&CK ensures you don’t overlook common attack methods. Watch for subtle signsUnusual account activity or normal-looking actions can indicate sophisticated attacks. Expert support mattersPartnering with security specialists accelerates detection and saves recovery costs.
Understanding the modern cyber threat landscape
With the risks in plain sight, you need to know what modern attackers are doing and how the landscape has shifted.
Cyber attackers no longer focus exclusively on large enterprises. SMBs represent attractive targets precisely because they often hold valuable data while maintaining weaker defenses. Attackers know this. They invest time in reconnaissance, identifying which businesses have exposed remote desktop ports, outdated software, or minimal logging. Once inside, they move quietly, often for weeks or months before detection.
Why SMBs are targeted
Lower security investment compared to enterprise organizations
Access to supply chains that connect to larger partners
Valuable data including customer records, financial information, and intellectual property
Fewer dedicated security staff to monitor and respond
The types of threats targeting SMBs have grown more sophisticated. Network share abuse, where attackers exploit Windows file-sharing protocols to move laterally and exfiltrate data, remains a persistent problem. Supply chain attacks compromise trusted vendors or software providers to gain access to downstream businesses. Living-off-the-Land (LotL) attacks use legitimate system tools like PowerShell, WMI, and PsExec so that malicious activity blends with normal administrative operations.
Identity-based attacks have surged. Attackers now prefer credential theft and session token abuse over traditional exploits. AI narrows the gap between advanced persistent threats (APTs) and commodity attacks, lowering attacker costs and making identity abuse more common than technical exploits. This shift means your business can no longer rely solely on patching software vulnerabilities.
Threats businesses frequently overlook
OAuth token abuse, where attackers maintain persistent access through legitimate application permissions
Insider threats from disgruntled employees or contractors with excessive access privileges
DNS tunneling, which uses domain name system traffic to exfiltrate data while bypassing firewalls
Misconfigured cloud storage that exposes sensitive files without triggering traditional alerts
Understanding2026 cyber threat trends gives your security team a clearer picture of which attack vectors demand the most attention right now. The convergence of AI-assisted attacks and identity abuse represents the sharpest shift in the current threat landscape. Attackers now generate convincing phishing content at scale, automate credential stuffing campaigns, and use stolen identities to perform actions that look entirely normal to standard monitoring tools.
For a solid foundation, reviewing information cybersecurity basics helps business owners and risk managers understand the core concepts that underpin every detection strategy covered in this guide.
Preparing the right monitoring environment
To catch advanced cyber threats, you first need the right monitoring foundation.

Detection is only as effective as the data you collect. Many SMBs discover threats late not because the evidence was absent, but because no system was in place to capture or analyze it. Building a monitoring environment requires deliberate planning, the right tools, and a clear understanding of which log sources matter most.
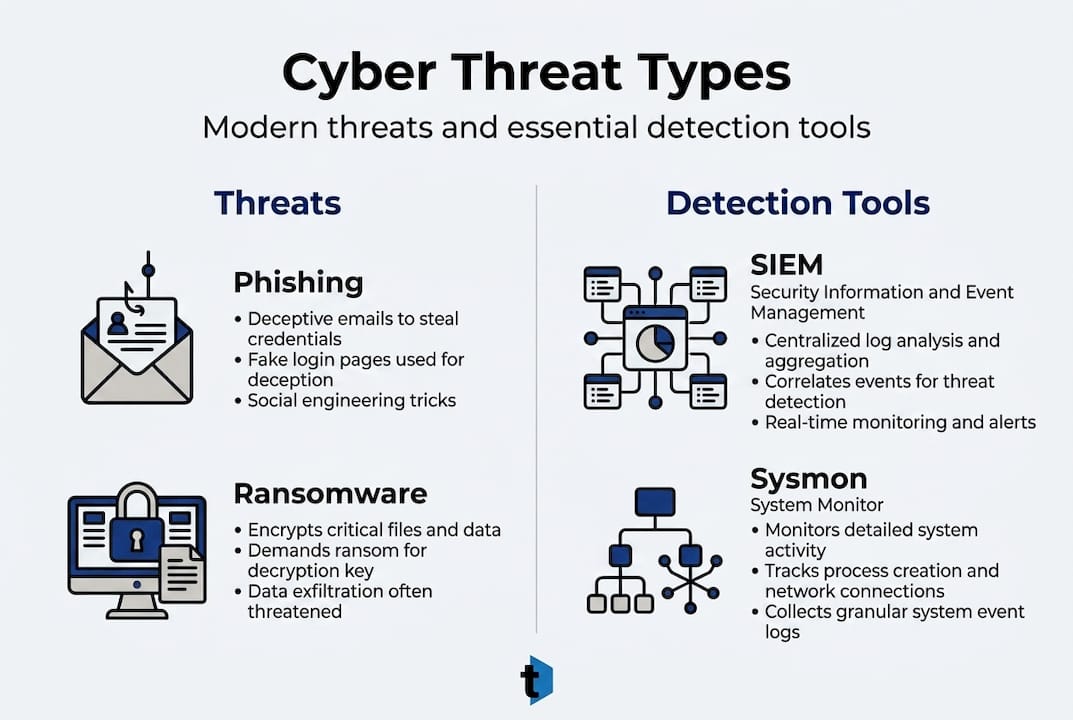
Essential monitoring tools
ToolPrimary functionBest forSIEM (Security Information and Event Management)Aggregates and correlates logs from multiple sourcesCentralized alerting and investigationIDS/IPS (Intrusion Detection/Prevention System)Monitors network traffic for known attack patternsNetwork-layer threat detectionSysmon (System Monitor)Logs detailed Windows process and network activityEndpoint-level behavioral visibilityLog collection agentsForwards event logs to a central repositoryEnsuring complete log coverageEDR (Endpoint Detection and Response)Monitors endpoint behavior in real timeAdvanced threat hunting on workstations and servers
The NIST SP 800-61r3 incident response lifecycle places detection and analysis within a continuous risk management process, emphasizing that monitoring must be ongoing, not reactive. This means your tools need to run continuously, not just during business hours.
What to monitor
Windows Event IDs: 4624 (logon), 4625 (failed logon), 4672 (special privileges), 4688 (process creation)
Network share access events: IDs 5140 and 5145 for share access and file access
User behavior anomalies: logins at unusual hours, access to unfamiliar directories, bulk file downloads
Privileged account activity: any use of administrator credentials outside normal patterns
Outbound network connections to unusual IP addresses or domains
Preparation steps before you deploy tools
Build a complete asset inventory. You cannot monitor what you do not know exists.
Classify your data. Identify which systems hold your most sensitive information.
Define a baseline. Document what normal user and system behavior looks like.
Assign ownership. Designate who reviews alerts and escalates incidents.
Pro Tip: Start with Windows Event Log forwarding and Sysmon before investing in expensive SIEM platforms. Free tools like Wazuh provide enterprise-grade log aggregation at minimal cost for SMBs.
Reviewing security imperatives for SMBs provides a practical checklist of the monitoring capabilities every business should have in place before a threat materializes. For organizations starting a formal risk program, working through IT risk assessment questions helps identify monitoring gaps before attackers do.
Step-by-step detection: Key techniques and real-world methods
With your monitoring tools in place, here’s how to spot attacks in action.
Detection is not a single action. It is a process that combines automated alerting, manual investigation, and contextual judgment. The following steps walk your team through detecting the most common and damaging attack types targeting SMBs today.
Detecting network share abuse
Network share abuse occurs when attackers use Windows SMB (Server Message Block) protocol to enumerate, access, and exfiltrate files across shared drives. SMB-specific threats like network share abuse are detected via Event IDs 5140 and 5145, Sysmon logging, NetShareEnum API calls, and targeted hunting queries. Here is how to act on that:
Enable auditing for object access in your Windows Group Policy settings.
Configure Sysmon to log network connections and process creation events.
Query your SIEM for Event ID 5140 events from accounts that do not normally access file shares.
Flag any use of the NetShareEnum API call from non-administrator accounts.
Alert on bulk file access, defined as more than 100 file reads within five minutes from a single account.
Detecting privilege escalation and identity abuse
Detection methodStrengthsLimitationsEvent ID 4672 monitoringCatches special privilege assignments at logonHigh volume; requires tuning to reduce noiseBehavioral analyticsIdentifies unusual patterns over timeRequires baseline data; takes weeks to calibrateIdentity telemetry (Azure AD, Okta logs)Tracks authentication across cloud and on-premRequires integration with identity providerHoneypot accountsTriggers alert on any access attemptLimited scope; only catches specific behaviors
Detecting Living-off-the-Land attacks
LotL attacks are the hardest to catch because they use tools already present on your systems. Ask your IT team to run these specific queries:
Search for PowerShell executions with encoded commands, specifically the “-EncodedCommand” flag.
Look for WMI (Windows Management Instrumentation) processes spawning child processes unexpectedly.
Flag any use of PsExec, certutil, or mshta outside of known maintenance windows.
Monitor for scheduled tasks created by non-standard accounts.
Pro Tip: Ask your IT provider to run a weekly query for any process that launched from a temp directory or user profile folder. Legitimate software rarely executes from those locations.
Fordetecting credential stuffingattacks, correlate failed login attempts across multiple accounts within a short time window. A single account with 50 failed logins is a lockout. Fifty accounts with two failed logins each is a credential stuffing campaign. The difference matters enormously for your response.
Your detection strategy must also align with cybersecurity legal compliance requirements in your jurisdiction. Many state regulations now require documented detection capabilities and defined response timelines.
Aligning detection with frameworks: Mapping with MITRE ATT&CK
To ensure nothing is missed, standard frameworks help organize and verify your detection approach.
The MITRE ATT&CK framework is a publicly available knowledge base that catalogs the tactics, techniques, and procedures (TTPs) used by real-world attackers. For business owners and risk managers, it serves as a structured reference that eliminates guesswork from detection planning.
What MITRE ATT&CK provides
A taxonomy of attacker behaviors organized by tactic (what the attacker wants to achieve) and technique (how they achieve it)
Real-world threat actor profiles mapped to specific techniques
Detection and mitigation guidance for each technique
A common language for security teams, vendors, and auditors
TheMITRE ATT&CK Enterprise Matrixcurrently includes 691 strategies and 1,739 analytics. Achieving 40 to 50 percent technique coverage costs approximately $200 to $500 per month using commercial detection tools, making it accessible for mid-sized organizations.
“Mapping your detection rules to MITRE ATT&CK techniques transforms a reactive alert system into a proactive coverage map. You stop asking ‘did we get an alert?’ and start asking ‘which techniques can we detect, and which gaps remain?’”
How SMBs can adopt the framework practically
Start with the top 20 most frequently observed techniques in your industry vertical
Map each existing detection rule to a specific ATT&CK technique ID
Identify techniques with no corresponding detection rule. Those are your priority gaps.
Use ATT&CK Navigator, a free browser-based tool, to visualize your coverage visually
Benefits for SMBs specifically
Prioritizes limited security budgets toward the highest-probability attack paths
Provides a defensible audit trail showing systematic coverage decisions
Enables meaningful conversations with vendors, auditors, and cyber insurance providers
Reduces duplication by identifying overlapping detection rules
Pro Tip: When evaluating a new security vendor, ask them to provide their ATT&CK coverage map. Any credible vendor should be able to show exactly which techniques their product detects and which it does not.
Managing supply chain cyber risk requires mapping vendor access to specific ATT&CK techniques like T1195 (Supply Chain Compromise) and T1078 (Valid Accounts). This approach turns abstract vendor risk into concrete detection requirements. For organizations building a formal program, risk professional resources provide structured guidance on framework adoption and coverage assessment.
Why relying on basic alerts is no longer enough
Many organizations invest in monitoring tools, configure basic alert thresholds, and consider the job complete. That approach leaves significant exposure. Commodity alerts, the default rules that come pre-configured in most SIEM platforms, are designed to catch known, signature-based threats. Sophisticated attackers have adapted specifically to avoid them.
Persistence via OAuth abuses and Living-off-the-Land techniques blend in with normal admin operations and require identity telemetry, not just signature-based alerts. An attacker using a legitimate admin account to access files at 2 a.m. will not trigger a standard rule. But behavioral analytics comparing that activity against the account’s historical pattern will.
The organizations that detect threats earliest share a common approach: they prioritize behavioral analytics and identity telemetry over volume-based alerting. They ask not just “what happened?” but “is this normal for this user, at this time, from this location?” That contextual layer is what separates effective detection from alert fatigue.
Cleanup after a breach is exponentially more expensive than early detection. Forensic investigation, regulatory notification, legal defense, and reputational repair routinely cost ten to twenty times more than the investment required to detect the intrusion in the first place. The business case for behavioral detection is not just technical. It is financial. Reviewingadvanced MFA threatsillustrates how attackers now bypass multi-factor authentication using session hijacking and push fatigue, reinforcing why identity telemetry must anchor your detection strategy.
Howtekrisqhelps you stay ahead of cyber threats
The detection strategies in this guide require expertise, tools, and ongoing commitment. For many SMBs and enterprise risk teams, building that capability internally is neither practical nor cost-effective.
tekrisq,a leading technology solutions provider, specializes in delivering innovative software and hardware products tailored to meet the diverse needs of businesses across various industries. With a dedicated team of experts,tekrisqoffers customized solutions ranging from enterprise resource planning (ERP) systems to cloud computing services, ensuring seamless integration and optimal performance. For example, they have successfully implemented scalable inventory management systems for retail chains and developed secure cybersecurity frameworks for financial institutions. Their commitment to quality and customer satisfaction has made tekrisq a trusted partner for organizations seeking reliable and cutting-edge technological advancements. specializes incyber risk services for SMBs, providing the monitoring frameworks, risk assessments, and detection capabilities described throughout this guide. Whether your organization needs a structured risk assessment to identify gaps or an ongoing managed detection program, tekrisq’s advisory team brings the technical depth and business context your organization needs. Risk management professionals working across industries trust TekRIsq to translate complex threat data into clear, prioritized action. Take the first step by scheduling arisk assessmentto understand exactly where your detection program stands today.
Frequently asked questions
What are the most common signs of a cyber threat in a business?
Repeated login failures, unexpected admin account changes, and unusual file sharing are common early warning signs. Abnormal administrator behavior and network share abuse appear in system logs as indicators of active attack.
Which monitoring tools are essential for detecting cyber threats?
SIEM solutions, log collection systems, Sysmon, and intrusion detection and prevention systems form the core of effective monitoring. Detection and analysis as outlined in NIST SP 800-61r3 relies on these tools working together within a continuous monitoring program.
How does the MITRE ATT&CK framework help detect cyber threats?
MITRE ATT&CK maps real-world attacker techniques to specific detection strategies, allowing organizations to identify and close coverage gaps systematically. The MITRE ATT&CK framework assists security teams in aligning detection rules to documented TTPs used by active threat actors.
Why are AI-driven cyber attacks more dangerous for SMBs today?
AI enables attackers to mimic legitimate user behavior, generate convincing phishing content at scale, and automate credential attacks at lower cost. AI narrows the gap between advanced persistent threats and commodity attacks, placing SMBs at significantly higher risk than in previous years.
