Should Your IT Guy Do the Cyber Risk Assessment?
Should Your IT Guy Do the Cyber Risk Assessment?
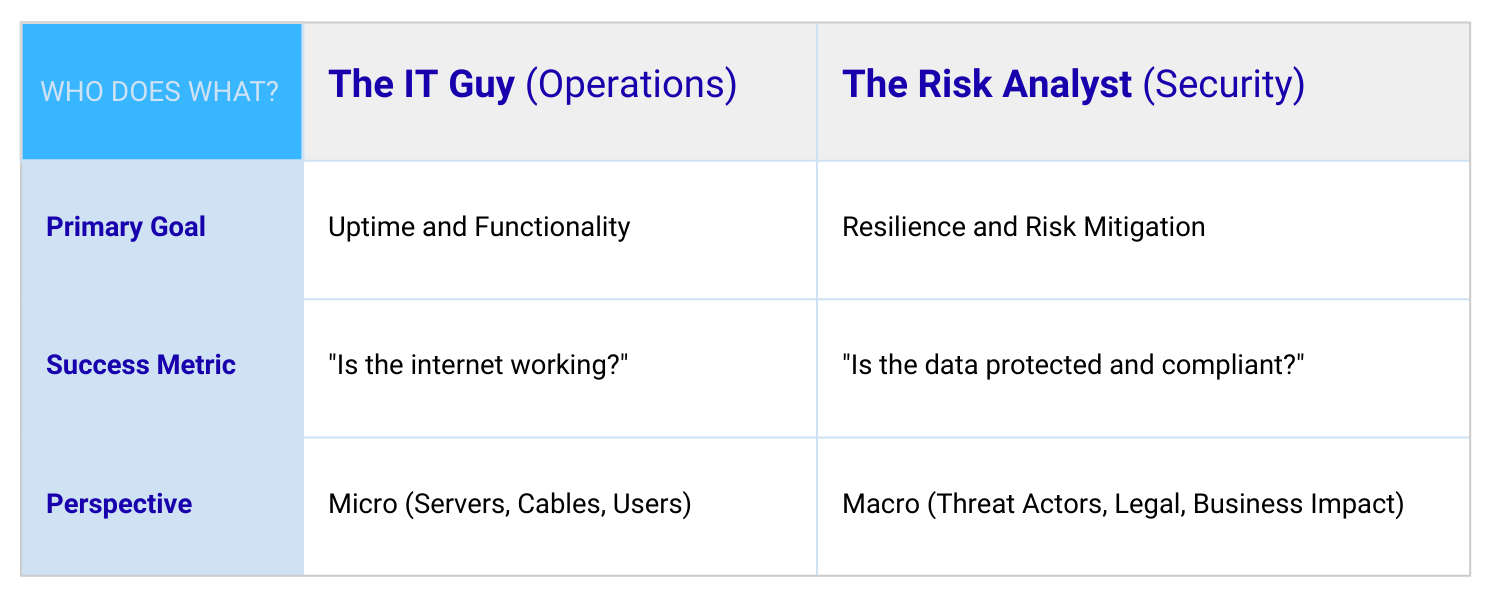
They Are Often Two Different, Distinct Disciplines
Do you have an internal IT team? In-house technicians who keep software running, troubleshoot networking problems, and install new hardware are invaluable. They often have deep knowledge of the systems and devices that keep the office functioning.
But are they the right people to bring the critical objectivity required for a cyber risk assessment?
Whether your IT staff is conducting the assessment themselves or participating alongside a third party, the answer is not always what you might expect.
Who Should Guide the Cyber Risk Assessment Process?
IT professionals without relevant, up-to-date cybersecurity training are often not the right people to lead a cyber risk assessment. There are several reasons for this.
Complete Objectivity
Internal IT teams frequently operate under pressure, balancing uptime, performance, and budget constraints. Many systems were configured quickly to meet business needs, not with every possible security implication in mind.
When asked to assess cyber risk, IT staff may unintentionally become defensive about decisions made in the past. In some cases, they may minimize weaknesses or demonstrate overconfidence about the organization’s cyber hygiene. This is understandable. Cybersecurity often competes with other IT priorities, and many common cybersecurity myths persist even among experienced technicians.
A cyber risk assessment requires independence and objectivity, not justification of past choices.
Fresh Relevance
While IT professionals may be familiar with general security concepts, cybersecurity threats evolve continuously. Modern ransomware, phishing campaigns, malware, and application-level attacks require constant study and monitoring.
Cybersecurity has become its own discipline, with specialized knowledge, best practices, and regulatory expectations. Protecting organizations against today’s threat landscape is a full-time responsibility, not a side task layered onto general IT duties.
Domain Expertise
Strong IT skills do not automatically translate into cybersecurity expertise. Managing devices, optimizing software, and supporting users are different from identifying systemic weaknesses, evaluating cybersecurity controls, and understanding how attackers exploit vulnerabilities.
Executives often assume internal IT staff can “handle cybersecurity.” This assumption can lead to gaps that only become visible after a serious incident. When a breach occurs, it is rarely due to a single mistake. It is usually the result of overlooked risks that were never independently evaluated.
Consider the following relevant, if not amusing anecdotes;
Culinary Comparison: Asking the IT Guy to do a Risk Analysis is like asking the line cook who made your steak to perform a comprehensive nutritional audit and FDA food safety inspection of the entire restaurant supply chain. He’s great at making sure the grill is hot and the order is out on time, but he isn’t exactly prepared to trace the E. coli risk back to a specific head of romaine in Yuma, Arizona.
Automotive Assumption: Asking a Formula 1 mechanic to write the global traffic laws and insurance liability tables for the next decade. Sure, he knows every bolt on the car and how to make it go 200 mph, but that doesn't mean he has any idea how to calculate the actuarial risk of a teenager texting in a school zone.
Structural Slip-Up: Asking the plumber who fixed your leaky sink to provide a certified hydrological impact study & flood-plain assessment for the county. He may be an expert at keeping water moving through the pipes; he doesn't necessarily know how to predict a 100-year storm or the legal ramifications of a dam breach.
Why an Independent Cyber Risk Assessment Matters
Cybersecurity professionals approach your environment differently. Their focus is not on performance or convenience. It is on whether bad actors can penetrate systems and how to reduce that risk.
An independent cyber risk assessment evaluates:
Whether existing cybersecurity controls are effective
How sensitive data is being protected
Whether regulatory and contractual requirements are being met
Whether incident response and recovery plans exist and are usable
Boards, lenders, and insurers increasingly require independent assessments as part of due diligence. These assessments also play a critical role in qualifying for cyber insurance coverage, as insurers continue to tighten underwriting requirements.
An assessment identifies gaps that must be addressed to become insurable and provides third-party confirmation that best practices are being followed.
From Prevention to Cyber Resilience
Cybercriminals constantly look for organizations that are complacent or overconfident. Staying ahead of them is a full-time job. Most businesses do not fail because they lacked technology. They fail because they did not understand their vulnerabilities.
The goal is not perfect prevention. The goal is layered defenses and cyber resilience, meaning the ability to withstand, respond to, and recover from incidents.
The only way to achieve that is to clearly understand where your risks exist.
Relying solely on internal IT staff, who already manage daily operations, is rarely the best strategy for gaining that clarity.
How tekrisq Helps Organizations Get It Right
tekrisq specializes in independent cyber risk assessments designed for small and mid-sized businesses. We focus on objectivity, relevance, and practicality.
Our assessments evaluate real-world risk, not just technical checklists. We help organizations understand where their cybersecurity controls fall short, how that impacts business operations, and what steps matter most.
Learn more about our approach:
To discuss your information security posture or schedule a consultation.
